Open-source lingua franca aims to let IoT devices and services communicate across manufacturers and operating systems.

Internet Of Things: 8 Cost-Cutting Ideas For Government
Internet Of Things: 8 Cost-Cutting Ideas For Government (Click image for larger view and slideshow.)
The big data vision of a global network of connected devices -- also known as the Internet of Things (IoT) -- is still a bit fuzzy with more than a few unresolved issues. For instance, too many devices communicate only with their manufacturers' private clouds. And when devices from multiple vendors can't share information, the IoT is pretty much DOA.
The AllSeen Alliance, a recently launched IoT consortium, hopes to bridge this communication gap by enabling IoT devices to share data -- regardless of manufacturer, brand, operating system, and other tech specs.
"While it's called the Internet of Things, it's really more like a bunch of devices talking to their own siloed Internets," said Liat Ben-Zur, chair of the AllSeen Alliance, in a phone interview with InformationWeek. "The thermostat talks to the thermostat's cloud, and the refrigerator talks to the refrigerator manufacturer's cloud."
The result: A big data Tower of Babel where devices from different manufacturers don't share data. Given the newness of the IoT concept, this isn't too surprising. But clearly there's work to be done.
"That's definitely not the vision the Internet of Things is supposed to be," said Ben-Zur.
[Learn how your house is getting smarter. See Internet Of Things Goes Home.]
One of the IoT's assumed attributes is the ability to get connected devices in businesses and homes to interact. The AllSeen Alliance's solution is AllJoyn, an open-source project that allows products, apps, and services to communicate via various transport layers -- including WiFi, power line, or Ethernet -- regardless of manufacturer or operating system, the Alliance claims.
"Any company that wants to leverage AllJoyn doesn't have to read a spec, interpret, and implement it," said Ben-Zur. "You just take the code, put it as-is into your product, and there's really not any interpretation needed. It will be the same code that everyone else gets."
The AllJoyn project was originally developed at Qualcomm, where Ben-Zur is a senior director of project management.
"Qualcomm has been working on this open-source project for several years," she said. "It started off as a peer-to-peer solution for smartphones and tablets to make it easier for app developers to build social experiences and games, without having to worry about complex issues associated with discovery, connectivity, and dynamic networks."
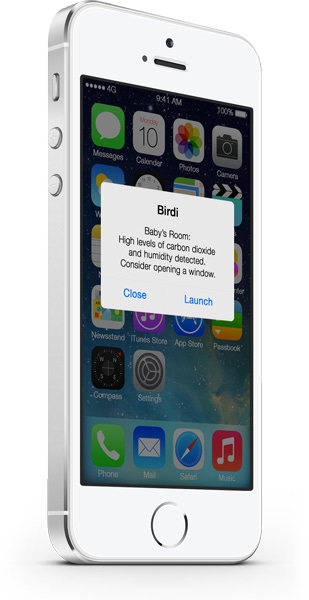
 Birdi, a smart air monitor that uses AllJoyn, communicates through smartphones, not loud beeps.
Birdi, a smart air monitor that uses AllJoyn, communicates through smartphones, not loud beeps.
The wireless telecom giant later expanded the project's goals, developing a broader, IoT-style implementation. Today, AllJoyn software runs on most major operating systems, including Linux (including the Linux-based Android), iOS, and Windows, including embedded variants.
"We realized this could be much more than software that goes onto phones, tablets, and computers. It could be more flexible to fit on any physical object -- from a light bulb, which has very limited processing power, or doesn't even run an OS, to appliances, routers, and everything in between," said Ben-Zur.
The AllSeen Alliance launched in December and currently has more than 40 members, including such well-known tech players as LG Electronics, Panasonic, Qualcomm, Sharp, Cisco, D-Link, and HTC. The group plans to announce more member companies in the coming months, said Ben-Zur.
A world of interconnected machines is a compelling concept, but how might a network of AllJoyn-enabled devices benefit the average business or consumer? Ben-Zur provided a home-based example, one the AllSeen Alliance demonstrated in January at CES in Las Vegas.
A smart air monitor from Birdi, a startup, was placed in a room with several other seemingly unrelated AllJoyn devices, including a television, speakers, light bulbs, and a door lock.
"These were devices from manufacturers that have never worked with Birdi before," said Ben-Zur.
"When the smoke detector detected smoke, it used the speakers to sound the alarm," she added. "So the home stereo was the alarm."
The connected light bulbs started flashing different colors -- a visual alert for the hearing-impaired. The television showed evacuation instructions, and the connected door unlocked itself automatically.
"It's a straightforward example, but you start to see the power of what happens when different devices speak the same language, and how seemingly disparate subsystems from different companies can come together," added Ben-Zur.
Join Enterprise Connect for an intensive day-long series of sessions in a free four-city road show focused on helping you design strategies for successful adoption and implementation of Microsoft's Lync. During this free program, we will help you evaluate Lync as a voice solution, address the challenges of integrating Lync into your existing UC architecture, and analyze total cost of ownership. Join your peers and leading vendor companies making Lync adoption possible in San Francisco, Chicago, Boston, and New York. Register for the Enterprise Connect Lync Tour today.
About the Author(s)
You May Also Like