A Government Accountability Office study recommends that agencies improve the way they respond to data breaches; new guidelines are en route.
A study of government data breaches is sparking a review of how agencies respond to incidents in which personal information is improperly exposed. New guidelines from the Office of Management and Budget (OMB) are expected to be phased in by the end of the year.
The Government Accountability Office study found that OMB guidelines for protecting personally identifiable information (PII) held in agency systems are incomplete and are not implemented consistently. As a result, agencies may not be taking corrective actions consistently to limit the risk to individuals from PII-related breaches.
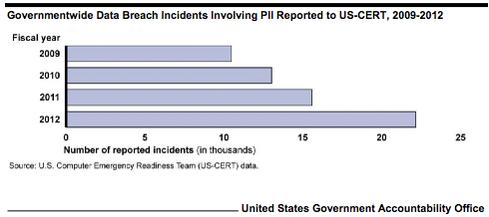
The number of PII breaches reported to the Homeland Security Department's US Computer Emergency Readiness Team (US-CERT) is growing steadily. There were 22,156 data breaches reported in fiscal 2012 -- a 42% increase from 2011 and a 111% increase from 2009. But the GAO found that requirements for quickly reporting these breaches could be doing more harm than good.
[Will 2014 be the year of change for the security industry? Increase Cyber-Security Workforce, Government Urged.]
The OMB requires breaches to be reported to the US-CERT within an hour of discovery, but it can take days to compile complete information on a breach. The US-CERT said it usually can do little with information reported in the initial hour, and the agencies reviewed in the study have not asked it for assistance in responding to breaches. As a result, these agencies may be expending resources to meet reporting requirements that provide little value and divert time and attention from responding to breaches, the GAO said.
The US-CERT's most significant role in government cybersecurity involves IT systems and networks. Given this limited role in dealing with PII breaches, the requirement to report all these incidents within an hour provides little value, especially in cases in which the data is encrypted or on paper, the GAO said. Consolidated periodic reporting of these incidents would be equally helpful and could free up resources that could be better used elsewhere.
The GAO recommended that the OMB update its guidelines to agencies to include the following:
Guidance on notifying affected persons based on the level of risk from the information exposed
Criteria for determining when assistance such as credit monitoring should be offered to affected individuals
Requirements for reporting PII-related breaches to the US-CERT, including revised timeframes and consolidated reporting of incidents that pose limited risk.
The Department of Homeland Security said it has begun working on the recommendations. Jim H. Crumpacker, the DHS liaison with the GAO, said the US-CERT has worked closely with the National Institute of Standards and Technology and has begun engaging with the OMB for the purposes of gathering requirements specific to these actions, and it will support the OMB in ongoing efforts to achieve the goals. New reporting requirements are expected to be fully phased in by Dec. 31.
The report also includes 22 recommendations to agencies, generally calling for better documentation of procedures for assessing the risk posed by a breach and notifying affected persons, as well as evaluations of breach responses so that lessons learned could be incorporated into policies.
The agencies reviewed for the report included the Centers for Medicare and Medicaid Services, the Department of the Army, the Department of Veterans Affairs, the Federal Deposit Insurance Corp., the Federal Reserve Board, the Federal Retirement Thrift Investment Board, the Internal Revenue Service, and the Securities and Exchange Commission.
William Jackson is a technology writer based in Washington, DC, who specializes in telecommunications, networking, and cybersecurity in the public sector.
Mobile, the cloud, and BYOD blur the lines between work and home, forcing IT to envision a new identity and access management strategy. Also in the The Future Of Identity issue of InformationWeek: Threats to smart grids are far worse than generally believed, but tools and resources are available to protect them (free registration required).
About the Author(s)
You May Also Like







