Federal IT leaders can foster cloud adoption by incorporating automated, repeatable security processes.
February 18, 2014

Top 10 Government IT Innovators Of 2013
Top 10 Government IT Innovators Of 2013 (Click image for larger view.)
The Federal Risk and Authorization Management Program (FedRAMP) has made important contributions to cloud security. However, FedRAMP focuses primarily on security compliance for public government cloud services. The approval process requires a lot of time and can hinder innovation and drive up costs.
However, FedRAMP leaders have an opportunity to enable -- not simply enforce -- faster government IT operations by fostering repeatable, high-quality, automated security operations -- in short, by championing a DevOps approach in government clouds.
In the 1980s, US manufacturing faced fierce competition from abroad, which forced a massive overhaul of manufacturing processes. That led companies to focus on new business practices, like Lean, Six Sigma, and Theory of Constraints, to eliminate process constraints and optimize costs. IT operations are undergoing a similar transformation today.
DevOps, automation, and the cloud are at the core of this IT revolution. DevOps integrates development and operational teams so they can solve problems faster. That's a cultural shift from previous IT practices. Combined with an automated cloud infrastructure, DevOps enables organizations to innovate and scale faster, usually saving significant costs.
[FedRAMP is changing the way cloud computing providers think about security. Read Cloud Providers Align With FedRAMP Security Standards.]
DevOps organizations often improve their cloud services hundreds of times a day, implementing improvements, responding to incidents, and making security fixes in minutes instead of days or weeks. This results in continuous delivery and a faster feedback loop -- or, as the military strategist Col. John Boyd called it, an OODA loop (observation, orientation, decision, action). A faster OODA loop is exactly what DevOps reinforces.
But to accomplish that, government certification and accreditation practices need to operate at the speed of the cloud. It does no good to be able to spin up creative cloud services quickly if the security approval process requires 6-12 months of cumbersome, expensive security paperwork -- possibly costing more than the actual monetary savings of the cloud project itself.
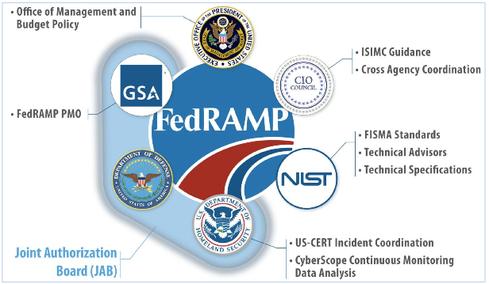
FedRAMP -- which is supported by IT leaders from the General Services Administration, the National Institute of Standards and Technology, the Office of Management and Budget, and several Cabinet departments -- could help every agency build secure government cloud solutions faster by creating automated, repeatable security processes and enabling accelerated responses to security incidents.
FedRAMP could start by modeling the open-source practices of DevOps leaders Netflix, Facebook, LinkedIn, Twitter, Amazon, and others, which use small, multi-disciplinary teams to build, improve, and release open-source cloud software components and frameworks continuously. From a security perspective, DevOps encourages embedding and constantly improving automated security practices at design time, making it easier to conduct continuous automated verification in production.
Adrian Cockcroft's FlowCon 2013 discussion does an exemplary job of outlining the DevOps practices and successes of the Netflix Open Source Software (OSS) Center. Many startups are using the center's software to accelerate their time to market within the cloud. Helen Bravo's discussion of the Open Web Application Security Project is another good source on the benefits of integrating DevOps with web application security to create a repeatable, ever-improving security framework.
FedRAMP or its partners could host and nurture an open repository of shared security and best-practice recipes (script modules) based on cloud automation standards. That would accelerate security compliance by allowing companies to import security recipes into their automation frameworks. FedRAMP could also accelerate compliance work, and lower its costs, by making key parts of the required security paperwork available.
If these recipes were available publicly, commercial entities could also use them to improve their security postures.
Here are a few leading automation options to consider:
OpenStack Orchestration (code name: Heat)
AWS CloudFormation and TestDrive
For a real-world example of how powerful automation recipes can be, look at an example from the consulting company Answers for AWS, which walks the reader through the process of setting up a complete Netflix OSS architecture in a few simple clicks. A FedRAMP model like this could enable repeatable, fine-grain security controls for various cloud architectures (email, websites, big data repositories) while decreasing human error, costs, and time to value.
It wouldn't be difficult to create a code repository. DevOps' open-source resources are often stored in GitHub, a powerful code management and collaboration repository, which is already being used by the US government. The president's executive order for an open data policy calls for releasing government policy in machine-readable format, but the policy itself was made an open-source resource on GitHub.
The Office of Management and Budget (OMB) followed this up by hosting Project Open Data in GitHub, which includes a series of open-source tools to make it easier for the government to release machine-readable formats. The GSA even provided open-source code for Data.gov in GitHub.
If you're looking to save time and effort on your government cloud project, you have a few options. You could start with Thomas McGonagle's Puppet NIST module in GitHub, which automates applying security policies in the NSA's Guide to the Secure Configuration of RedHat Enterprise Linux 5.
If you want more of a head start, you might consider using Buddha Labs' hardened Amazon Machine Images, which come with full security compliance audit reports. They were developed by Vincent Passaro, founder of Buddha Labs. Passaro is a highly certified security expert who understands the Defense Departments Information Assurance Certification Accreditation Process firsthand. He makes building and documenting a security compliant system in the cloud as easy as possible.
But agencies would clearly benefit if FedRAMP and its partner agencies seized the opportunity to improve operational security practices. The question is whether the FedRAMP community will remain cloud controllers or become cloud enablers.
Find out how a government program is putting cloud computing on the fast track to better security. Also in the Cloud Security issue of InformationWeek Government: Defense CIO Teri Takai on why FedRAMP helps everyone.
About the Author(s)
You May Also Like







