Cybersecurity
business people gathered around a chalkboard table with words Start Up
Cyber Resilience
Maximizing Security and Minimizing Cost: Tips from a Startup Cybersecurity ProMaximizing Security and Minimizing Cost: Tips from a Startup Cybersecurity Pro
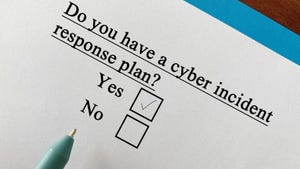
Investing in cost-effective cybersecurity practices is not just good from a security standpoint -- it's also a smart startup business move.
Never Miss a Beat: Get a snapshot of the issues affecting the IT industry straight to your inbox.