DARPA Targets Counterfeit Electronics
Defense Advanced Research Projects Agency's SHIELD program aims to develop a method to authenticate electronic components.

10 Cool DARPA Projects In Development
10 Cool DARPA Projects In Development (Click image for larger view.)
The Defense Advanced Research Projects Agency (DARPA) is looking to develop a tool to verify the trustworthiness of electronic components. Counterfeit parts present a huge risk for the Department of Defense (DOD), where malfunctioning electronics can lead to system failures, the agency said. The challenge of detecting counterfeit or compromised components has also grown more complicated as manufacturers rely on an increasingly complex web of parts suppliers and contractors.
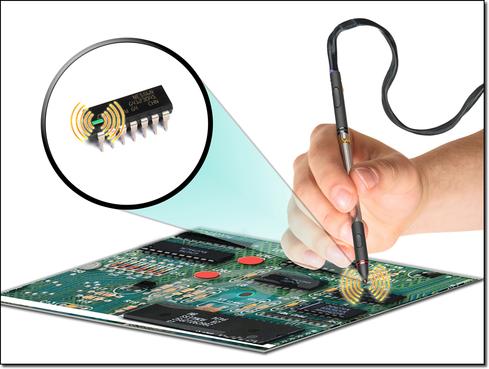
A new DARPA program, called Supply Chain Hardware Integrity for Electronics Defense (SHIELD), will focus on the creation of a small component, or dielet, for authenticating electronic parts at any step of the supply chain. The agency is seeking proposals that would "revolutionize electronic authentication with potential scalability and advanced technology not available today."
According to a notice posted Feb. 21, DARPA is interested in hardware that contains a full encryption engine and sensors to detect tampering, and that has the ability to attach to current electronic components such as microchips.
[DARPA also wants a way to remotely destroy military electronics. Read IBM Develops Self-Destructing Chips For DARPA.]
DARPA said the dielet would be inserted into an electronic component's package at a manufacturing site or attached to existing components. Authenticity testing could be performed anywhere with a handheld probe, which would need to be close to the dielet for scanning. A smartphone, or another low-cost appliance, could be used to upload a serial number to a central server. The server would send an unencrypted challenge to the dielet, which would then send back an encrypted answer and data from passive sensors, indicating tampering.
Technology resulting from the SHIELD program would guarantee protection against threats related to counterfeit electronics, such as recycled components that are sold as new, according to DARPA. Other threats include unlicensed overproduction of authorized components or components that failed tests.
The technology would also help identify and reject sub-standard components that have been sold as though they were of higher quality or which have been labeled with a newer date of manufacture. Additionally, SHIELD technology would protect against clones and copies -- often of low quality -- and parts that have been repackaged for unauthorized applications.
"The dielet will be designed to be robust in operation, yet fragile in the face of tampering. What SHIELD is seeking is a very advanced piece of hardware that will offer an on-demand authentication method never before available to the supply chain," DARPA program manager Kerry Bernstein said in a written statement.
The tool would cost less than a penny per unit, yet it would make counterfeiting too expensive and technically difficult, said Bernstein. Although the program is funded by DARPA, it will be up to the industry to adapt future implementations to "make the technology scalable to the industry and the Defense supply chain," he added.
According to announcement, SHIELD will usher in new industry and government standards for component authentication and supply-chain risk management.
DARPA will hold a conference on March 14 to discuss details with potential program participants.
Find out how a government program is putting cloud computing on the fast track to better security. Also in the Cloud Security issue of InformationWeek Government: Defense CIO Teri Takai on why FedRAMP helps everyone.
About the Author(s)
You May Also Like







