Feds Pursue Cloud Forensics Standards
NIST identifies 65 challenges that forensic investigators face in gathering and analyzing digital information stored in the cloud, seeks help developing standards to aid law enforcement.

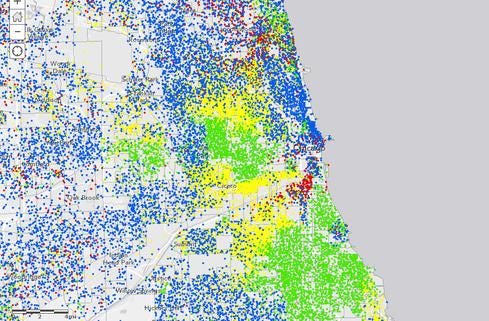
Government Data + Maps: 10 Great Examples
Government Data + Maps: 10 Great Examples (Click image for larger view and slideshow.)
The National Institute of Standards and Technology has released a draft report for public comment that sets forth the daunting challenges forensic examiners face in tracking down and using digital information stored in the cloud.
The draft report, "NIST Cloud Computing Forensic Science Challenges," sets forth 65 challenges of cloud forensics divided into nine categories that a working group drawn from the government, private sector and academia has identified in the course of its examination of the challenge.
"The long-term goal of this effort is to build a deeper understanding of, and consensus on, the high-priority challenges so that the public and private sectors can collaborate on effective responses," said Martin Herman, co-chairman of NIST's Cloud Computing Forensic Working Group.
[Time to get serious? Read Federal Agencies Must Get Practical About Cloud.]
The study is the catalyst for a focused effort to produce standards that will aid and facilitate cloud forensics in support of U.S. criminal and civil law and related security endeavors.
Cloud forensics involves applying digital forensic science in cloud computing environments to reconstruct past events through identification, collection, examination, and interpretation of digital evidence collected.
The target audience for the study consists of digital forensics examiners and researchers, cloud-security professionals, law enforcement officials and cloud auditors. In a larger sense, though, the study also is directed at cloud policy makers and cloud service consumers.
The cloud creates unique challenges for digital forensic investigators, the report states.
"While the goals of first responders and forensic examiners may be the same in the cloud context in comparison to large-scale network forensics, distinctive features of cloud computing, such as segregation of duties among cloud actors, inability to acquire network logs from the load balancer or routers, multi-tenancy, and rapid elasticity introduce unique scenarios for digital investigations," the report states.
The difficulty of digital forensics with regard to virtualization, large-scale data processing, and the proliferation of mobile devices become even more formidable when those aspects must be addressed in a cloud computing environment, the report states.
The working group gathered an impressive amount of data, which is presented in considerable depth on spread sheets for each of the 65 challenges. The group intends the spreadsheet to serve as a living document that will evolve as stakeholders identify potential technologies and standards that would be useful and practical for addressing each of the challenges.
The nine major groups by which the challenges were categorized in the report are architecture, data collection, analysis, anti-forensics, incident first responders, role management, legal, standards, and training. Anti-forensics are a set of techniques used to intentionally prevent or misdirect forensic analysis, such as obfuscation, data hiding, and malware.
The working group holds that the technical challenges must be fully understood so that technologies and standards-based mitigation approaches can be developed to address them and ensure forensic investigators are able to achieve a high rate of success.
In addition to an ongoing dialog with those interested in the topic, the working group will prioritize the challenges, determine gaps in technology, standards, and measurements as they pertain to the challenges, and develop a plan of action to address the gaps.
NIST believes there is a pressing need to develop forensic protocols that major cloud providers eventually would adopt. "These protocols must adequately address the needs of the first responders and court systems while assuring the cloud providers no disruption or minimal disruption to their services," the report states.
Comments on the draft report are due by July 21 and should be submitted using the comment template for NISTIR 8006.
Fully 75% of 536 respondents say their orgs are as or more vulnerable to malicious code attacks and security breaches compared with a year ago. And in the face of a crushing skills shortage, 40% subsist on no more than 5% of the IT budget. Where do we go from here? Get the Research: 2014 Strategic Security Survey report today (registration required).
About the Author
You May Also Like






