Two-Minute Toolkit: CloudSphere on Cybersecurity and Offboarding
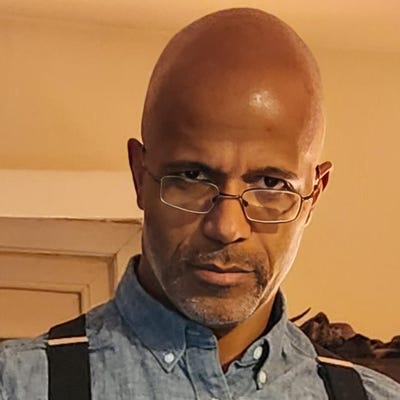
Technical Evangelist Keith Neilson talks security considerations that may come up as a company parts ways with an employee.
.jpg?width=1280&auto=webp&quality=95&format=jpg&disable=upscale)
What happens to a former employee’s digital access after they have parted ways with a company? Sorting out what clearances they had and then ensuring those rights and privileges are dealt with accordingly is a necessary part of offboarding a departing employee.
The worst-case scenario might be a vindictive ex-employee tries to exploit their knowledge and privileges to enact some sort of harm on their former employer--whether that means exposing or stealing sensitive data or opening the door for malware to be deployed. There might also be unintended cybersecurity breaches that stem from third parties who discover exploitable access and permissions, left open and forgotten after the departure of a former employee the hacker does not even know.
Keith Neilson, technical evangelist at CloudSphere, shares insights on the necessity for mindful diligence in cybersecurity when offboarding employees as they depart their companies.
About the Author
You May Also Like