Secret Service Seeks Social Signals: Inside The RFP
Social media analytics RFP seeks to sort serious from sarcastic threats against government officials.
The Secret Service wants to get smarter about social media, so it's soliciting proposals from the many social media monitoring and analytics companies that help organizations understand what's being said about them. In the case of the Secret Service, the agency also might like to know about any violent or threatening comments addressed to President Obama and others under its protection.
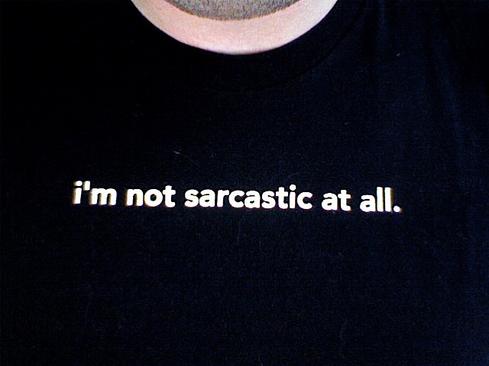
A request for proposals popped up this week on FedBizOpps.gov. Reports from Nextgov, The Washington Post, and other publications all highlighted one particular requirement on the list -- that the system be able to detect sarcasm. (Okay, I have to say it: yeah, right.)
A Secret Service media spokesperson made a point of emphasizing to the Post that sarcasm detection was just one of many requirements on the agency's list (see the longer list below). What the RFP actually asks for is the "ability to detect sarcasm and false positives," an aspect of the text analytics subdiscipline of sentiment analysis, which as a whole is still very much a work in progress.
Sentiment analysis is an important component of social media monitoring because national brands (including those of politicians and government agencies) generate too large a volume of tweets, posts, and comments on news stories for each one to be studied individually. Analytic software can help by sorting through thousands of posts to identify positive or negative keywords and phrases. Lacking life experience, however, computer algorithms often miss the subtleties.
Depending on context, the phrase "Yeah, great service," could be either praise or a stinging indictment. Sentiment analysis tools will sometimes get the context wrong, judging a negative comment as a positive. Whoever evaluates responses to this RFP will have to seek out the best of the bunch rather than a perfect performance.
[Want to see an early "prototype" of the Secret Service's sarcasm detector? See Geekend: Sarcasm Detector Wanted.]
Why is this important to the Secret Service?
"The Service also wants to be able to have an automatic way to determine if social media users are potentially violent or if they are just joking with their posts," concluded one report on the conservative news and opinion blog Breitbart.com. "It is unclear just how much Congress knows of this new Secret Service contract."
I think that's jumping to conclusions, beyond what's spelled out in the RFP. I jumped to the very same conclusion, although I wouldn't put the sinister shading on it that this might be something for Congress to look into. Seems to me the Secret Service ought to have as much insight into the swirl of social media sentiments as Proctor & Gamble or any other firm doing social media market research. P&G doesn't have to worry about assassins or wannabe assassins, just competition from Unilever. People say very nasty things about the President and other top officials every day on blogs, news sites, and social media. Most of it is just talk, and some of it is sarcastic, but I'd like to think someone is watching out for patterns of more serious, threatening talk and planning.
On the other hand, if that was the monitoring program's primary purpose, the requisition might have come out of the Secret Service's National Threat Assessment Center. Instead, the solicitation is coming from the Office of Government and Public Affairs.
Just as likely, the goal is to monitor and protect the health of the Secret Service's own brand. For example, they might want to watch for reports of Secret Service agents caught drunk or consorting with prostitutes -- and hope that they're not real.
The RFP states that the agency wants the chosen tool to automate the monitoring process, handle large sets of social media data, identify statistical patterns, visualize complex data for clear, concise presentation, and be usable by multiple staff members.
Specific requirements:
Real time stream analysis
Customizable, keyword search features
Sentiment analysis
Trend analysis
Audience segmentation
Geographic segmentation
Qualitative data-visualization representations (heat maps, charts, graphs, etc.)
Multiple-user access
Functionality to have read-only users
Access to historical twitter data
Influencer identification
Standard Web browser access with login credentials
User-level permissions
Compatibility with Internet Explorer 8
Section 508 compliant
Ability to detect sarcasm and false positives
Functionality to send notifications to users
Functionality to analyze data over a given period of time
Ability to quantify the agency's social media outreach/footprint
Vendor-provided training and technical/customer support
Ability to create custom reports without involving IT specialists
Ability to search online content in multiple languages
Cyber-criminals wielding advanced persistent threats have plenty of innovative techniques to evade network and endpoint defenses. It's scary stuff, and ignorance is definitely not bliss. How to fight back? Think security that's distributed, stratified, and adaptive. Read our Advanced Attacks Demand New Defenses report today. (Free registration required.)
About the Author
You May Also Like






