Ukraine Cybersecurity Message at BlackBerry Security Summit
A surprise livestream from the besieged country, and other speakers, gave a look at ways cybersecurity can affect tangible issues in the physical world.
7 Slides

Already have an account?
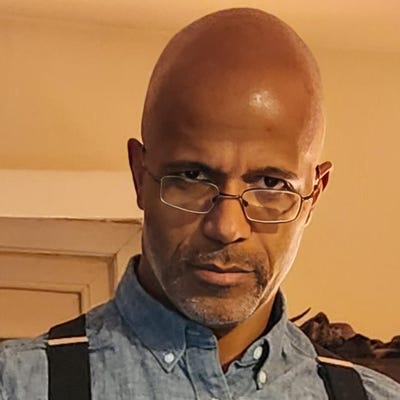
Victor Zhora, deputy chairman of the State Service of Special Communications and Information Protection of UkraineJoao-Pierre S. Ruth
-
About the Author
Never Miss a Beat: Get a snapshot of the issues affecting the IT industry straight to your inbox.
You May Also Like
More Insights