NIST Security Guidance Revision: Prepare Now
NIST 800-53 Revision 5 will likely put more emphasis on continuous monitoring. Don't wait until it arrives to close your security gaps.

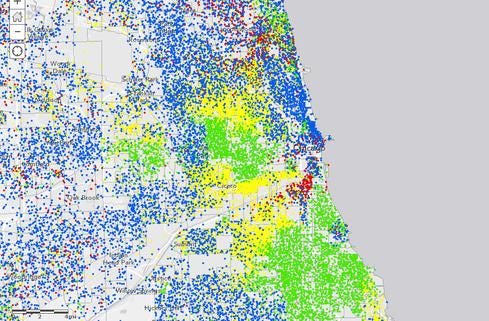
Government Data + Maps: 10 Great Examples
Government Data + Maps: 10 Great Examples (Click image for larger view and slideshow.)
The National Institute of Science and Technology's Special Publication 800-53 aims to raise the bar and set a standard of security for federal government information processing systems. As NIST works on Revision 5 of the document, which I expect to come out in early 2015 (see editor's note in the comments section), it will need to reverse the sweeping generalizations made in Revision 4 regarding the nature of the threat against data. Network defense is not a spectator sport -- it must be engaged in continuously and consciously.
As a natural evolution of the NIST document, continuous monitoring and anomaly detection will likely play a more significant role in Revision 5. However, agencies should not wait until next April to shift focus towards understanding the specific threats to data through continuous monitoring. There is a great deal agencies can do to get a head start on the guidance and to prepare their systems and networks for the new version in advance.
Build an active defense
The rubber meets the road in active defense at strategic data acquisition -- collecting the information needed to understand the changing nature of the adversary. For a multi-faceted data acquisition approach, we must start by analyzing the key threat categories that we face.
The term "advanced persistent threat" has been overused in recent years, but it describes the most important type of attacker any government agency should prepare for. Government organizations are by definition the only high-valued target in their class -- after all, there is only one IRS or one Defense Department -- so there is no other "low-hanging fruit" for attackers to go after. This means targeted attackers will be stealthy and crafty in any offensive approach.
[Ready to respond? GAO Faults Agencies On Cyber Incident Response.]
Another prevalent, yet avoidable, data threat is simple user error. The sheer number of data loss cases where documents were inadvertently emailed, laptops were left on airplanes, or phones were lost is staggering -- and growing. These mistakes are often inconsequential, but all it takes is an observant attacker to pay close attention to the careless worker and take advantage of the opportunity. Understanding the attacker means understanding his or her options.
Currently, the NIST document's focus is heavily weighted towards the mapping and classification of key data assets. This is important because it helps security analysts explore the landscape that needs to be defended. However, Revision 5 should also take into consideration that effective defense against data sabotage or espionage requires a thorough understanding of the data assets, as well as an intimate knowledge of the adversary.
Understand your adversary
Analyzing the adversary is accomplished by collecting as much information as possible about it. Data acquisition is the process of intelligence-gathering on the adversary.
Data acquisition is different from simply monitoring your networks. Monitoring provides a limited-time view of the status of your infrastructure and focuses on uptime. Intelligence-gathering requires advanced and widely deployed telemetry and focuses on security. This provides the operator a long-term, historical view (months to years), and also a 360-degree view of the infrastructure. Active network defense involves watching and understanding data access patterns, common log messages, and traffic endpoints, in order to build an understanding of what is going on and keep a finger on the pulse.
The next revision of NIST 800-53 will likely emphasize intelligence-gathering through data acquisition and policy creation based on attacker knowledge. The recommendations will shift focus from simple data inventory management to risk assessment, in order to understand adversary behavior and specific threats to this data better. Long-term storage and analysis of network traffic records, logs, authentication information, and the behavior of traffic patterns will become a more prominent theme.
With this we will see a shift towards enabling the analyst to become more active and effective at defending the information infrastructure. This will come both in the form of policy creation and threat and adversary analysis.
NIST is on the right track. We cannot simply focus on the data alone. No general can defend his or her territory without a thorough understanding of the adversary. You must understand your enemy -- and then some. The trick here is that NIST releases a new set of guidelines only every so often, so businesses should look beyond this occasional checklist and be proactive when it comes to protecting their data.
NIST's cyber security framework gives critical-infrastructure operators a new tool to assess readiness. But will operators put this voluntary framework to work? Read the Protecting Critical Infrastructure issue of InformationWeek Government today.
About the Author(s)
You May Also Like
How to Amplify DevOps with DevSecOps
May 22, 2024Generative AI: Use Cases and Risks in 2024
May 29, 2024Smart Service Management
June 4, 2024







