FDA Pushes To Improve Medical Device Security
Cyber attacks pose a grave threat to the integrity of healthcare services, agency says.

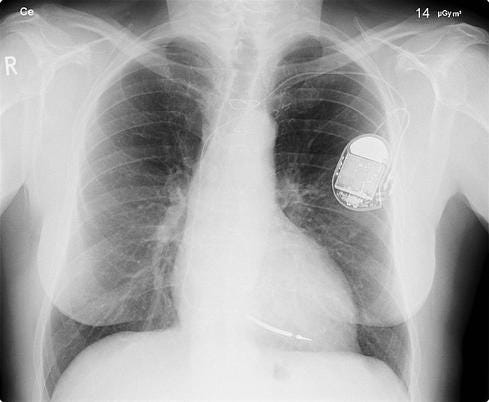
Hackers Outsmart Pacemakers, Fitbits: Worried Yet?
Hackers Outsmart Pacemakers, Fitbits: Worried Yet? (click image for larger view)
When former VP Dick Cheney last year disclosed that doctors had disabled the wireless capabilities in his pacemaker because of hacker concerns, it hammered home the dangers posed by network-connected medical devices. Such concerns have finally prompted the US Food and Drug Administration (FDA) to convene a collaborative industry-wide effort to bolster medical device cyber security.
As a first step, the FDA will host a workshop in Arlington, Va., next month during which it hopes to bring together medical device manufacturers, healthcare providers, biomedical engineers, IT systems administrators, health insurers, and others. The goal of the two-day event is to spur a discussion on the best ways to identify and mitigate cybersecurity vulnerabilities in commonly used medical devices.
Cyber vulnerabilities can cause device malfunction, disrupt critical healthcare services, and provide improper access to protected patient information, the FDA announced Tuesday.
"Advancing medical device cybersecurity measures within the HPH Sector relies upon a 'whole of community' approach that will require acceptance of a 'shared ownership and shared responsibility' model," the agency said in a note announcing the workshop.
[Boosting cyber security in healthcare requires strong leadership. Read Healthcare Needs Cyber Security Leadership & Governance.]
Cheney's disclosure and several high-profile hacking demonstrations have raised considerable concern over medical device insecurities in recent years.
In one demonstration, late security researcher Barnaby Jack showed how a wireless-enabled insulin pump from a leading vendor could be remotely manipulated to deliver a deadly dose of the drug to a patient wearing the device.
In another exploit, Jack showed how a malicious attacker could take remote control of a wireless-enabled pacemaker and get it to deliver a lethal shock. Other security researchers, such as Jay Radcliffe (a diabetic himself), have also demonstrated how medical devices can be manipulated by taking advantage of easily exploitable security holes.
While such exploits have garnered the most attention, medical devices are vulnerable to other cyberthreats as well. The most pressing ones are those that affect device availability and integrity, according to a report in the Association for the Advancement of Medical Instrumentation. Many problems stem from the fact that critical medical equipment often runs obsolete and unsupported software.
"One of the challenges to improved cybersecurity and therefore safety and effectiveness is a lifecycle mismatch," the authors of the report noted. "For instance, operating system software with production lifecycles measured in months does not match well with a medical device having production lifecycles measured in years or decades."
The FDA's goal is to address such issues through a collaborative process involving multiple stakeholders in the healthcare industry. A major focus of the effort is to get the industry to identify cyber security vulnerabilities, especially on end-of-life legacy systems. The FDA also wants the industry to develop security standards and benchmarks for medical devices as well as a common way to identify, assess, and mitigate vulnerabilities in medical products.
Richard Stiennon, principal at security consulting firm IT-Harvest, called the FDA initiative somewhat ironic.
"The FDA is actually at fault for the widespread vulnerabilities in medical devices," Stiennon said. "They instituted a regulatory process requiring device manufacturers to certify things like heart rate monitors, heart lung machines, oxygen metering -- and the software running on them." The certification process has tended to be expensive and time-consuming, he added, resulting in many systems not being updated or patched on a regular basis.
The owners of electronic health records aren't necessarily the patients. How much control should they have? Get the new Who Owns Patient Data? issue of InformationWeek Healthcare today.
About the Author
You May Also Like






