NSA Gives Assessment of Cyber Threats from Russia, China, and AI
International adversaries present ever more aggressive risks to cybersecurity while generative AI might accelerate attacks -- and possibly defense efforts.
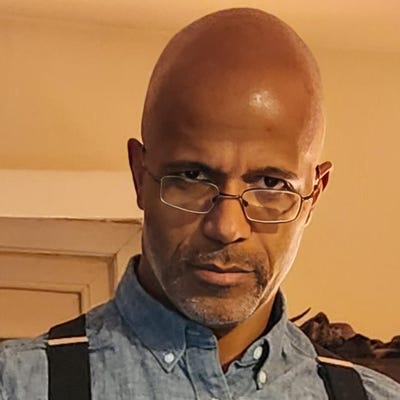
Nation states are engaging in increasingly belligerent, malicious cyber activity, according to Rob Joyce, director of cybersecurity with the NSA.
That was some of the perspective he offered about bad actors in his “State of the Hack” presentation at the RSA Conference in San Francisco last week, outlining recent and ongoing cyber threats.
Top of mind for Joyce and the NSA this year is the continued conflict in Ukraine, where Russia persists in real-world and digital assaults on the country. “There were more than 2,000 attacks from Russia in 2022, and over 300 were against the defense and security sectors,” he said.
Some 400 cyberattacks against Ukraine targeted civilian infrastructure, telecom, finance, and energy, according to Joyce. More than 500 cyberattacks were aimed at government entities that are not part of defense. “That’s more than 10 cyberattacks a day going across a broad swath of the infrastructure,” he said.
As of 2023, Joyce said, Ukraine was reporting more integrated cyber and “kinetic effects” -- in other words, the hacking efforts were being coordinated with military attacks.
There are three types of cyberattacks being seen primarily, Joyce said, in the conflict:
Intelligence collection to prosecute the war
Disruptive activity to break down civil society
Hacktivist activity from supporters of Russia’s aggression
He cited the GRU, Russia’s foreign military intelligence agency, has been the predominant actor in such digital aggression. “Ukraine has been a GRU target for many, many years,” Joyce said and referred to the Sandworm attacks on the electric grid in 2015, and 2016 as well as the NotPetya attack in 2017. Then in early 2022, on the eve of the war, WhisperGate malware defaced some 70 Ukraine-based websites.
“They were saying, ‘Be afraid and expect the worst,’” he said.
Facing a Pacing Threat
Switching to another nation-state watched by the NSA, Joyce referred to China as a “pacing threat” for this country. “It is the past, present, and future challenge for the US,” he said. The use of cyber activity by China, Joyce said, is a long-term investment for a marathon-like strategy as part of an overall espionage campaign. “They are strategic, agile, brazen, innovative, and enduring,” Joyce said. “They have goals in quantum computing; they have goals in big data; they have goals in artificial intelligence, pharmaceuticals, health care, medicine, and military technologies.”
Companies in those sectors, he said, should expect to face cyber intrusions from the People’s Republic of China.
Nations that neighbor China have also been targeted by such hacking efforts, Joyce said, including the Association of Southeast Asian Nations and member nations -- as reported by Wired in February. The intent, Joyce said, is to gather intelligence and influence the region around China, against friends and enemies alike.
Domestic information control and repression within China have long been part of the government’s operations, he said, particularly through standards bodies, which can also affect technology and security internationally.
As Joyce explained, China has been very participatory in setting standards, in essence stacking the deck for technology and resources on the global scene that do not support US standards for security and privacy. “We’re seeing coordinated efforts across the PRC companies to counter the US or Allied proposal standards,” he said, “and drop into the standards a competitive edge for the Chinese technologies.”
For example, Joyce said, Huawei and China Mobile have proposed technologies they want to drive in places they can assume chair positions on voting bodings for standards -- while shooting down security technology improvements from the US. “We personally have had at NSA proposals inside these standards bodies that have been pushed back on simply because they’re US origin,” he said.
AI Might Be a Boon to Defenders and Bad Actors
Apart from those nation-state concerns, the NSA has also been watching the explosion of artificial intelligence and machine learning, Joyce said. “This truly is some game-changing technology that’s emerging.”
When it comes to generative AI, he is focused on three areas:
How adversaries might pick up on the technology and what they might do with it
What defenders can do to utilize AI and machine learning in effective ways
What can be done in a maligned way to poison trust in things that rely on AI and machine learning
Though Joyce does not expect AI, in the near term, to be able to exploit all three areas, he did express concerns about adversaries integrating generative technology or other AI tech into their workflow. That could help them outpace people who do not use such resources. “It’s going to reduce the cycle time and the dwell time of attackers.”
So, AI may accelerate the capabilities of bad actors, but it might also support defenders as well.
“Buckle up,” Joyce said. “I think the innovation cycle on the development and the innovation cycle on people creating use cases to execute with it is going to be really rapid.”
What to Read Next:
What Does the National Cybersecurity Strategy Mean for Public and Private Stakeholders?
Is It Time to Start Worrying About Quantum Computing Security?
About the Author
You May Also Like