The Convergence Of 3G/4G And Wi-Fi
As carriers off-load traffic to WLANs and hotspots, IT needs to mind security and performance.
October 19, 2011

U.S. carriers see Wi-Fi as necessary to manage rapidly escalating data demand, and they're shifting users to 802.11 networks when possible. As they do, enterprise IT teams must keep tabs on unified security and encryption, how these handoffs can cut costs, and the way the still-crude movement between 3G/4G and Wi-Fi affects employees.
Yes, it's one more thing on an already crowded plate of concerns, but mobile broadband use is increasing faster than carriers can keep up. More than 500,000 mobile applications are available across superfast networks, and Cisco projects data demand will almost double annually for the next five years. The problem is that today's cellular networks simply don't have sufficient capacity to handle all this traffic. So, to motivate users to limit their data use over cellular 3G and 4G networks, operators have introduced tiered plans where pricing is usage-based on cellular connections but free on Wi-Fi.
For companies that are paying by the gigabyte, using Wi-Fi instead of 3G/4G should translate to lower costs--and potentially let them adopt less expensive plans--if some questions can be resolved. They include: What happens when users switch networks in midsession? Which networks should different applications have access to? How do we address security and management?
It's also an evolving environment, with the way cellular networks hand off to Wi-Fi poised to change over the next several years as vendors implement new standards like the Next Generation Hotspot (NGH) initiative, a.k.a. Hotspot 2.0. We discuss these in depth in our full report on 3G/4G and Wi-Fi convergence, available free with registration.
Control Issues
Operators don't particularly want to off-load to Wi-Fi. It's easier to manage the user experience when all traffic is on their cellular networks, but they don't have a choice. The nature of wireless is that it has inherently lower capacity than wire, and wireline is what's setting broadband expectations. Streaming content, in particular, generates massive amounts of traffic. In response, operators are using more efficient 4G technologies, deploying as many cell sites as possible, acquiring spectrum as it's doled out, and consolidating (as in the case of the proposed AT&T/T-Mobile merger) in pursuit of greater system efficiency.
Yet, even all this isn't enough. So Wi-Fi, which provides a tremendous capacity boost via a significant amount of radio spectrum that's separate from expensive cellular spectrum, is the answer for now.
AT&T is particularly aggressive with off-loading data to Wi-Fi. On smartphones, if Wi-Fi is turned on, the devices will automatically connect to AT&T hotspots at locations such as Starbucks or certain airports. T-Mobile also has a large hotspot network, as does Verizon. However, only AT&T and T-Mobile include hotspot service for free with both laptop modems and smartphones. Verizon's Wi-Fi hotspot service is free for laptops with its 3G/4G service but isn't available for smartphones. Sprint doesn't offer hotspot service, though with its announced move from WiMax to LTE, that may be on the horizon.
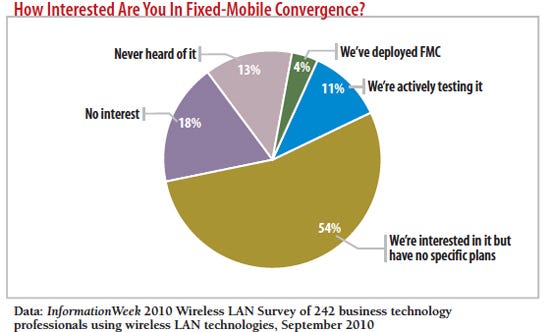
On the enterprise side, our InformationWeek 2010 Wireless LAN survey showed little interest in fixed-mobile convergence systems that seamlessly hand off calls. Just 4% had deployed FMC in their companies, and 11% were testing it.
Strategy: 3G/4G & Wi-Fi Convergence
 Our full report on 3G/4G and Wi-Fi convergence is free with registration.
Our full report on 3G/4G and Wi-Fi convergence is free with registration.
This report includes 15 pages of action-oriented analysis. What you'll find:
Why enterprise IT teams should keep an eye on the 3GPP IFOM specification
The lowdown on Sprint's move from WiMax to LTE
Static On The Line
The good news is, to protect their network capacity, most operators offer a variety of tiered pricing plans. Since business applications typically don't generate that much data, you may be able to shift employees to less-pricey service plans, especially if they have access to the enterprise WLAN for much of their work.
Be aware, however, that data usage varies tremendously. In our experience, there's no such thing as a "typical" user. So, before deciding whether a 2-GB-per-month service plan is sufficient, IT must understand its applications. Email, Office document downloads, database lookups, and static Web pages won't add up to much data. But throw in video-based training, field service procedures, or video-enhanced VoIP, and use can skyrocket. That's when select use of Wi-Fi makes a lot of sense.
As good as the savings yielded by increased use of WLANs may be, though, matters aren't that simple. The WLAN or hotspot is essentially a separate network, which means performance and security differ and data sessions are separate. What's more, an employee may not even be connecting to the Wi-Fi network you expect.
Consider this scenario: Your CFO is at the airport waiting for a flight. She sees that the Dow Jones has gone up 300 points that morning and decides it's a good time to unload some stock. She's got 15 minutes before she must board the plane--plenty of time to whip out her laptop, connect to the airport's free Wi-Fi, and execute the transaction, right? But every page takes a minute to load. When she tries to finalize the transaction, the page freezes. It's now five minutes before boarding, so she terminates the Wi-Fi link and brings up a 3G connection via her Android smartphone, with the phone acting as a Wi-Fi hotspot for the laptop. In two minutes she easily completes the transaction.
Then she fires off an email to IT complaining about the laptop's poor performance. Your first thought: I hope no one was eavesdropping on that airport hotspot.
Let's begin with the performance issue. It used to be that a Wi-Fi connection was always preferable to a 3G connection. But 3G/4G networks are much faster than they used to be, and many Wi-Fi networks are slower than they once were because of congestion. 4G LTE networks today can easily deliver 5 Mbps to 10 Mbps downlink speeds. Meanwhile, many hotspots, including at a Starbucks where we did some ad hoc testing, are constrained by T1 backhaul circuits that limit throughput to 1.5 Mbps. Add to the mix a dozen caffeine-buzzed smartphone, tablet, and laptop users, and performance can go down from there in a hurry.
Contributing to this problem, the Wi-Fi implementations in smartphones and tablets tend to be no-frills. Even if they support 802.11n, throughputs are well below the 100- Mbps and higher rates that users might get with their laptops. A typical tablet achieved a maximum transmission rate of only 15 Mbps. That means IT must ensure that the infrastructure compensates for the limitations of mobile devices. This could mean either installing access points that have improved radio performance (such as better interference rejection) to enable more reliable connections over longer distances or installing more access points to alleviate congestion, particularly in places where mobile workers congregate.
Safety First
As for hotspot networks, they don't offer any form of encryption, so traffic is vulnerable to eavesdropping and other attacks, such as session hijacking. Cellular networks aren't necessarily the best when it comes to security, but they're generally far better than Wi-Fi. Most 3G connections employ 128-bit encryption as well as mutual authentication between devices and networks. The catch is that 2G networks are much less secure, and enterprises have no control over whether employees are connected via 2G or 3G. Even if the air link is encrypted, data is encrypted only to a node within the operator network, after which it flows in the clear.
For these reasons, establishing secure communications over cellular networks generally requires use of a VPN. The same VPN link that protects the cellular connection can protect the Wi-Fi connection.
But this leads directly to another complication. When a device hands off from cellular to Wi-Fi, it has to drop the data session and re-establish one with a different IP address. For some applications, such as Web browsing or email, this isn't a big problem, except if it happens mid-download. But for session-oriented communications, such as a VoIP call, it will likely cause the call to terminate. This disruption will also break most VPN connections, requiring the user to reconnect. Fixing this problem requires a special mobile VPN, such as Mobility from NetMotion Wireless, where the VPN provides a separate IP address to the computer than the one the network provides, and allows persistent connections even as the underlying network changes. Because applications are insulated from the network, this architectural approach also allows application sessions to persist even if devices are temporarily beyond network coverage.
Burning Through Bandwidth
Another question is how to control what application accesses what access medium. Enterprise applications like email don't consume that much data, but what's to stop an employee from watching The Walking Dead over 3G during lunch on his smartphone? Short of an actual zombie apocalypse, not a thing.
To control costs, some IT teams we work with restrict bandwidth-hogging applications such as video to Wi-Fi connections. Otherwise, users could quickly burn through their data plans. Without some form of policy enforcement, though, like that provided by mobile device management systems from Good Technology, MobileIron, NetMotion Mobility, and Sybase Afaria, IT has little control over how users consume data, or on what network. Even with MDM, policy enforcement is complicated when IT has to support employee-provided devices that span multiple platforms.
And even if we could get all data traffic off 3G and onto enterprise WLANs when employees are on site, that still wouldn't solve all of our problems. 3G data consumption may go down, but now there's an increased load on the WLAN. If the enterprise network was designed with the minimum number of access points, or 100- Mbps Ethernet instead of 1-Gbps Ethernet for backhaul, IT might have to beef up the WLAN to accommodate new mobile device traffic.
Still, we expect most IT teams would rather invest in their own networks than hand those dollars over to an operator in overage charges.
Finally, as Wi-Fi networks proliferate and operators implement automatic handoffs to hotspots, a new type of problem could emerge: Namely, what Wi-Fi network should the device connect with, especially when several are available? The device could see an operator-provided hotspot and automatically connect with it, even though there might be an alternate Wi-Fi network that IT would prefer using. Perhaps that alternate network has better security or performance. We don't see this as much of a problem yet, but be aware of the algorithms devices use to connect to ensure that they're compatible with IT requirements. For now, the answer is education; usually the order in which Wi-Fi networks are presented in the connection management configuration screen is the order in which connections are made. Ensure that users know to avoid potentially insecure links.
Today's challenges with 3G/4G and Wi-Fi may be annoying, but they're largely manageable. And, thanks to various new specifications, things could get a lot better. The bad news is that it may take years for these improvements, which we discuss in our full report, to fully come online. In the meantime, forward-looking IT teams should plan accordingly. Wi-Fi integration will become more seamless and more secure, and connectivity may consume less power. Until then, pay attention to policies, consider an MDM suite if you don't have one, educate users, and provide mobile VPNs where appropriate.

InformationWeek: Oct. 31, 2011 Issue
Download a free PDF of InformationWeek magazine
(registration required)
You May Also Like




